Impact Analysis
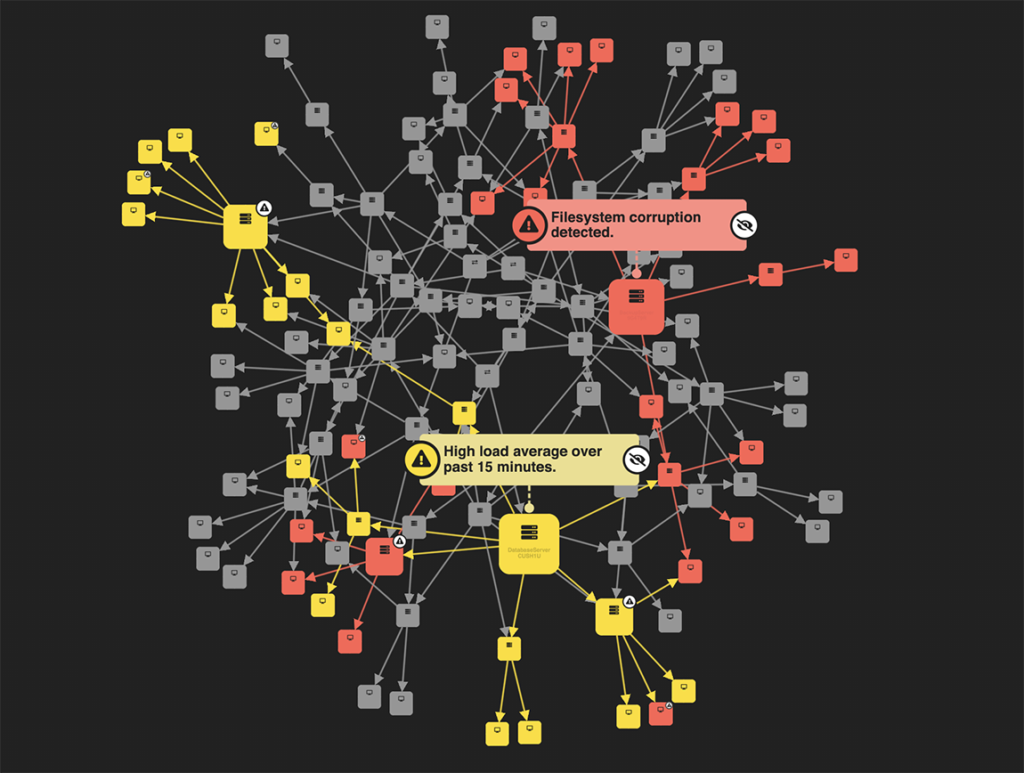
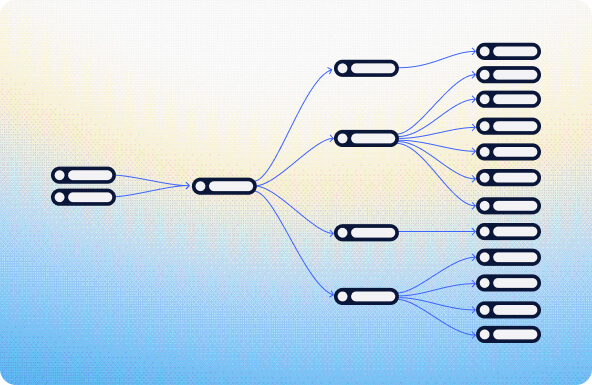
Hover over a node to explore its dependencies and select it to change the view to a hierarchy of its dependents.
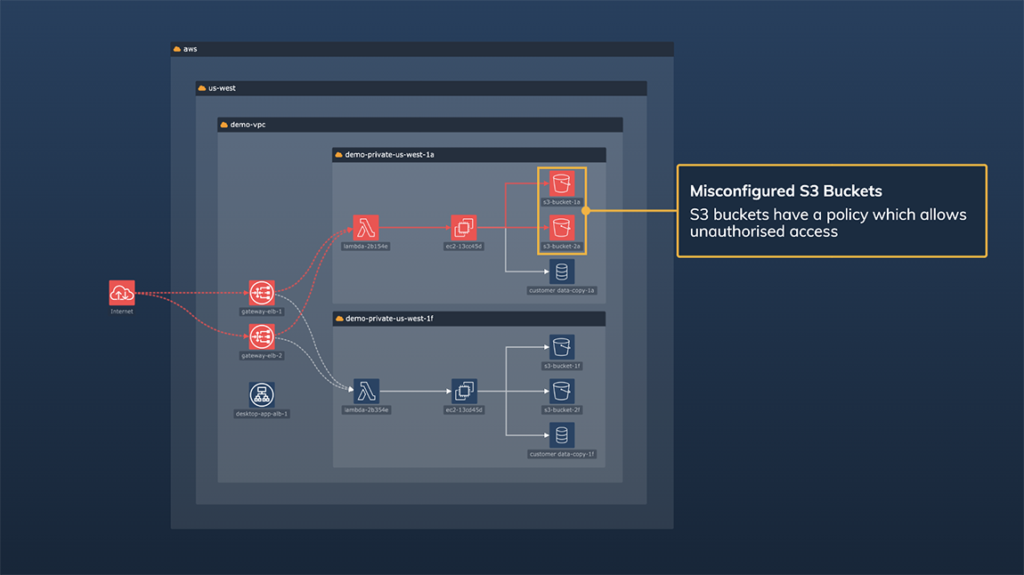
Cloud security
Alternate between different cloud infrastructure views, and a focussed view of an attack path.
Make sense of complex cybersecurity data with interactive graph, timeline and geospatial visualization. Help analysts investigate and respond to threats faster with visual tools purpose-built for cyber workflows.

Trusted by 250+ organizations worldwide
Cyber threat analysts face an immense challenge: big, noisy, fast-moving data from cloud infrastructure, identity systems, endpoints, agentic activity, applications and open-source intelligence.
Thousands of alerts are generated every day but only a fraction matter, and failing to spot the right signal fast enough means real organizational risk.
Visualization is how teams regain control and cut through volume and complexity, making it easier to:
This domain pulls together the key cyber workflows where interactive intelligence – delivered through graph, timeline and geospatial visualization – powers speed, clarity, and better decisions.
Map what assets, identities and environments you have and how they are connected.
Understand where you’re exposed before attackers exploit it.
Identify suspicious activity and emerging threats within complex, high-volume data.
Give users visualization tools that help them move from discovery to decision – and decision to action.
Our SDKs are trusted by enterprises and loved by startups.






Deliver high-impact, fully customizable visualizations that turn complex cybersecurity data into intuitive, differentiated user experiences your customers remember.
Transform detected alerts into clear, interactive views that add context and explain impact so teams can prioritise and act with confidence.
Support your AI models with visual context that make insights easier to trust, investigate and communicate.
Combine network and timeline views to help users move from isolated alerts to complete understanding of events, dependencies and impact.
Fully control styling, interaction and UX so your product reflects your brand and meets the expectations of your customers.
Deploy high-performance visualizations proven in cybersecurity platforms that handle large, complex datasets without compromising usability.
Try these interactive demos in your browser.
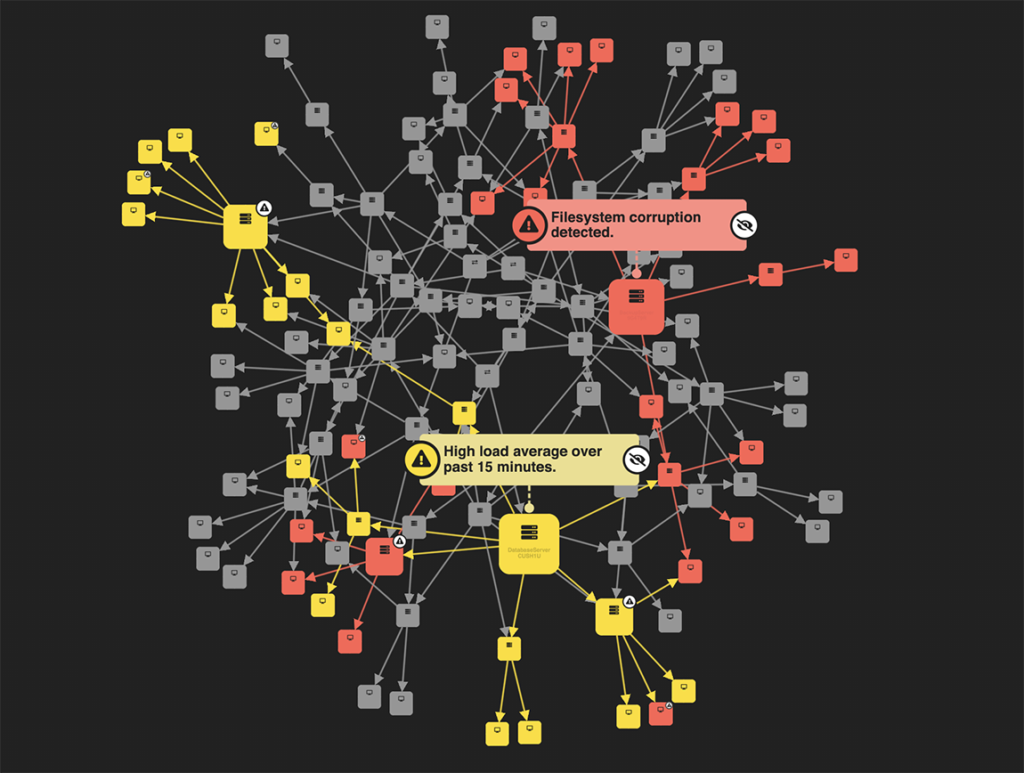
Hover over a node to explore its dependencies and select it to change the view to a hierarchy of its dependents.
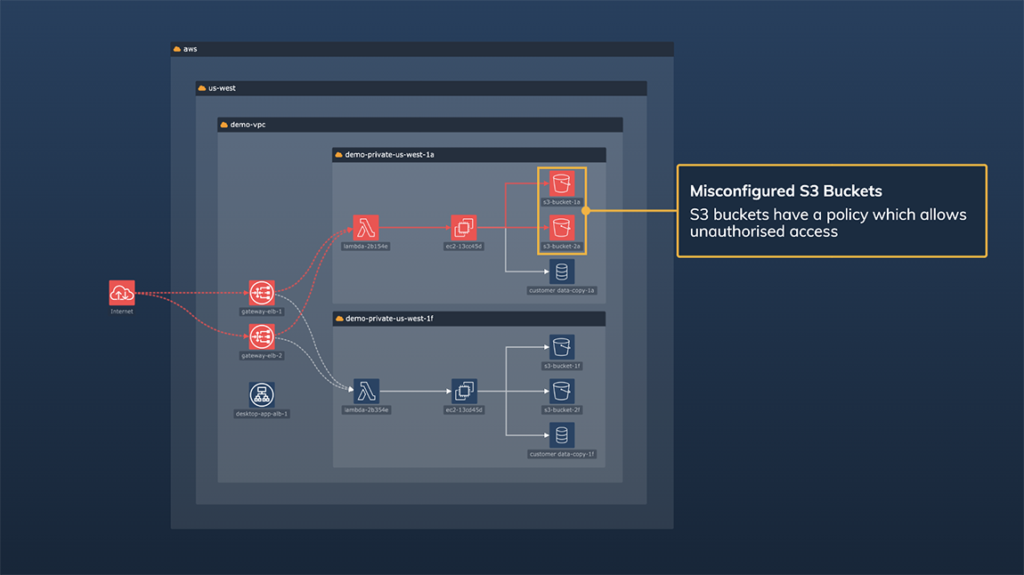
Alternate between different cloud infrastructure views, and a focussed view of an attack path.
Anything with entities, relationships or temporal events – including alerts, logs, cloud assets, identity data, threat intel feeds, MITRE ATT&CK mappings, and more.
Graph and timeline views reduce noise by exposing patterns, clusters, anomalies and sequences that matter, helping analysts focus on high-impact events faster.
Fully. You can tailor layouts, styling, interactions and UX to match your application and user needs, whether for an analyst-heavy SOC or a commercial UI.
Yes. We offer sample code, MCP server, API reference and full documentation to speed up development.